Kubernetes Dashboard
Read more about our Kubernetes automation services
ML AI LLM AI Agents DevOps MCP n8n Kubernetes Setup Hybrid Cloud(Oracle) Enterprise Networking - HP & Cisco VMware Fortinet Setup Azure Cloud Docker Website Design Automated pipeline that monitors FortiGate firewall logs
We provide end-to-end IT consultancy from Ground Up starting with end-user specializing in the convergence of traditional networking and modern cloud-native orchestration. Whether you need Desktop end user Support or are building from the ground up or migrating to the cloud, We bridge the gap between physical hardware and automated workflows.
Completed Work & Production Projects: Ground-up deployment and support of Traditional Network Infrastructure. Full-stack physical setup including Cisco/HP Layer 3 switching, VLAN segmentation, Subnetting, and DHCP management.
Deployment and management of Windows Servers, including Active Directory (ADDS), Domain Controllers, and DNS configurations.
Execution of Fortigate Firewall SD-WAN -load-balance traffic between multiple internet connections or failover automatically if one goes down.implementation: defining Security Policies, configuring SSL VPNs, and securing Remote Desktop (RDP) environments.
Deployed SAN storage and Virtualization infrastructure using VMware ESXi, managing VM hosts via vSphere.
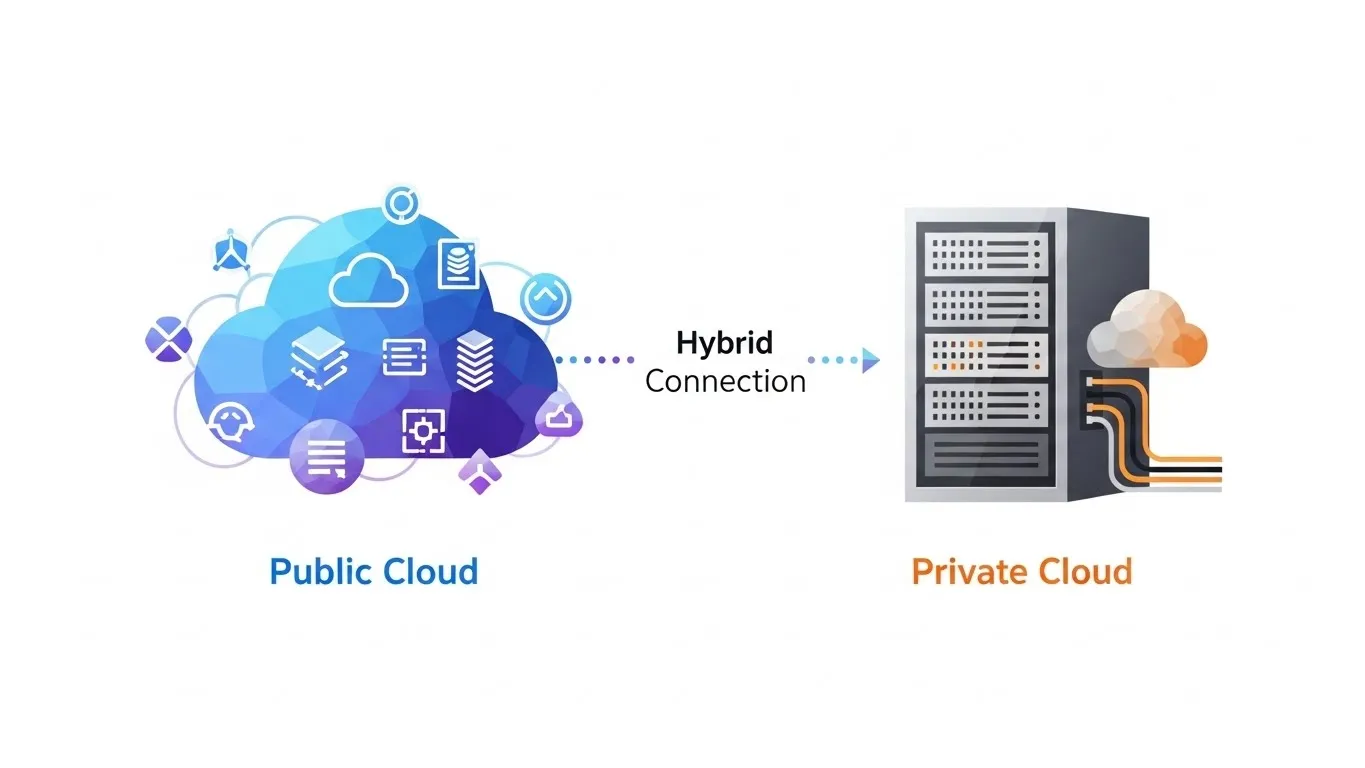
Designed resilient hybrid clusters (On-prem + OCI), container orchestration with K8s, and automated AI workflow integration via n8n to monitor Fortigate for intrusions.
Advanced resource deployment and management across AWS, Azure, and Oracle Cloud Infrastructure (OCI).
Full-Stack Web Development (Front-end & Back-end): Delivered complete production websites including www.sypheit.cloud and www.uzamarket.com.
* Note: All these Production Projects are also mirrored in my Home Lab.
We don’t just manage software; I understand the entire stack. From the physical Layer 3 switch and the hypervisor to the Kubernetes worker node running your AI workflows, I ensure your infrastructure is secure, scalable, and automated.
My work is backed by a sophisticated production-grade lab environment that mirrors enterprise challenges:
Hybrid K8s Cluster: Mastering control planes on-prem with worker nodes scaling in OCI
Storage Solutions: High-availability SMB file sharing within containerized environments.
AI Integration: Custom-built n8n containers driving intelligent business logic.


"Empowering businesses with resilient hybrid cloud architectures, enterprise-grade networking, and intelligent automation—from the physical switch to the Kubernetes cluster.".
Infrastructure Support, Hybrid Cloud & Kubernetes Orchestration
Intelligent Workflow Automation (AI & Low-Code) - Leveraging the power of AI to automate manual business processes through containerized automation engines

Managing the compute resources required for AI-driven applications within OCI..
L3 Network Design: Ground-up configuration of Cisco and HP Layer 3 switches.

n8n Implementation: Building custom, self-hosted AI workflows within your Kubernetes environment.

Stop fighting legacy limitations. Whether you need a Cisco CCNP veteran to stabilize your on-premise core or a DevOps Architect to scale your Hybrid Cloud and AI workflows—I build the bridges that get you there.
Syphe iT - CLOUD, DEVOPS, AI MANAGED SERVICES
SYPHE IT

SYPHE IT
SYPHE IT

SYPHE IT

SYPHE IT
$$$$$$$$$$$$$$$$$$$$$
"Working with Syphe IT was a game-changer for our infrastructure. They didn't just provide a service; they architected a robust, secure environment that seamlessly bridged our on-premise hardware with the cloud. Their expertise in FortiGate security and hybrid networking gave us the confidence that our data is protected by enterprise-grade protocols. Professional, insightful, and highly technical."
Q: How do you ensure secure communication between on-premises hardware and cloud resources?
ReadMore on Fortgate Advanced setup
A: My methodology assumes all traffic is untrusted by default. I configure firewall policies that block all inbound and outbound traffic, only explicitly allowing the specific ports, services, and IP ranges required for your business operations. This drastically reduces the attack surface and prevents unauthorized lateral movement within the network.
A: Yes. I have extensive experience in multi-vendor interoperability. This includes configuring standard protocols like 802.1Q (Trunking), OSPF/EIGRP for routing, and LACP for link aggregation to ensure that different hardware brands communicate seamlessly and maintain high availability.
A: While a standard firewall filters traffic based on ports and IP addresses (Layer 3 & 4), the IPS I configure performs Deep Packet Inspection (DPI) at the application layer (Layer 7). This allows us to detect and block specific exploit signatures, such as RDP brute-force attacks or SMB vulnerabilities, even if the port itself is open for legitimate use.
A: I implement VLSM (Variable Length Subnet Masking) to maximize IP efficiency. By segmenting the network into logical VLANs (e.g., Servers, Workstations, IoT, Guest), I can apply granular security policies while ensuring that the address space is utilized effectively without wasting IP ranges.
Securing Your Network: A Step-by-Step Guide to FortiWifi 60E IPS and SSL VPN.
 December 12
December 12